GROpinion
[Opinion] How To Pull Nigeria From The Brink
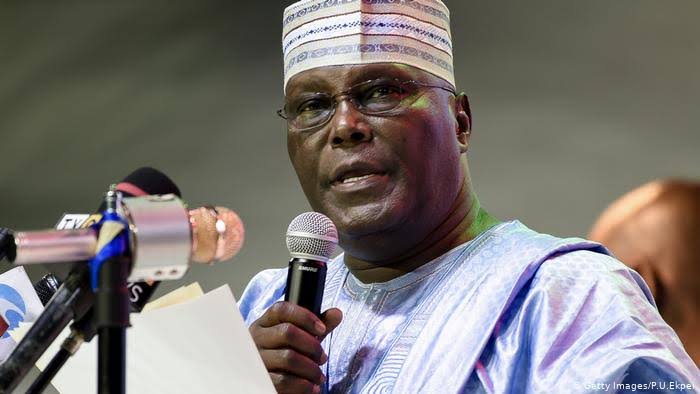
By Atiku Abubakar.
On Monday, April 27, 2020, British oil and gas giant, BP, became the latest in a growing number of energy firms to declare a massive quarterly loss. Their loss was in the region of $4.4 billion dollars. Bear in mind that this was a conglomerate that posted a $2.6 billion profit in the corresponding quarter of 2019.
The challenges that are already engulfing the oil and gas sector will continue to plague that industry for at least the rest of the year, and may reach apocalyptic levels sooner than we expect.
As I write this, there are hundreds of crude oil laden ships, all filled up, with nowhere to berth, and accruing daily charges of an average of $30,000.
We have also seen crude oil prices plunge to record lows, to the extent that some variants of the product have been given out for free, or worse still, producers have paid storage facilities to take their products.
As at today, Nigeria is pricing its very low sulphur sweet crude at $10 per barrel, yet buyers are balking. Our sweet crude is becoming a little bitter.
I had earlier warned that Nigeria needs a Strategic Reserve to store unsold crude. Now, we have so much crude and no one to buy it, nowhere to store it, and little idea what to do with it.
Barely three years ago, I had also alerted that the “crude thinking” promoted by our dependence on crude oil will lead to a rude shock.
“If you are still talking about oil, you are in the past. As far as I am concerned, the era of oil is gone. If you want to believe it, believe it. If you do not want to believe it, you will see it. It is crude thinking to continue to talk and base development projections on crude oil”, I had said at a public event in the nation’s capital.
We must face the fact that reliance on crude oil is failing Nigeria and other mono product economy crude oil exporters. Now is the time for Nigeria and her contemporaries to cure their addiction to sweet crude. For far too long we have grown high on our own supply, to the extent that we have neglected almost every other sector of our economy.
This present rude awakening should be seen as a blessing in disguise – a blessing that compels us to take those drastic actions that will free us from the crude oil trap.
We need to diversify our economy, and yes, it is easier said than done, but that does not mean it is an impossible task.
Prior to Nigeria’s October 1, 1960 independence from Great Britain, not only were we a nation self reliant in food production, but we also exported food to other countries, earning precious foreign exchange in the process. Who can forget the great groundnut pyramids in Northern Nigeria? For example, in 1957, agriculture formed a whopping 86% of our export revenue. By 1977, agricultural exports had dwindled to 6%, and today, the figure is less than 3%.
How did our country go from being a net exporter of agricultural products to a net importer of food products? How did we go from a country that could feed itself to one that desperately depends on foreign imports for survival? The answer to these questions is leadership focus.
During elections, Nigerian politicians spend a significant amount of their campaign time discussing how they will manage the nation’s resources. However, the fundamental difference between a leader and a manager is that while a manager focuses on managing existing resources, a leader sets out a creative vision which the country must follow to chart a course to political and socio-economic greatness.
Certainly, what is abundantly clear is that Nigeria is never going to become an industrialized nation by selling more oil, even if the oil market recovers. The lessons from Venezuela’s current predicament come to mind. If oil and gas could have saved any nation, that nation would be Venezuela. Unfortunately, Venezuela is bankrupt and insolvent.
Saudi Arabia, despite its huge reserves and a highly publicized listing of Saudi Aramco, is feeling the pinch and working rapidly towards its Vision 2030, which requires Saudi Arabia to diversify from its dependence on Oil. Other prudent countries facing the same predicament are doing the same.
Oil economies need to learn a thing or two about economic diversification from the United Arab Emirates. Despite being a young nation, the leadership of the UAE has managed to diversify the economy of this country from an almost complete reliance on oil in the 1970s, to a country where 72% of the GDP comes from the non oil sectors of the economy such as aviation, tourism and services sectors.
In Nigeria, our diversification should embrace agriculture as the primary sector earmarked for development, because agriculture is a low hanging fruit, is key to ensuring food subsistence, and with the recent signing of the African Continental Free Trade Area agreement (AFCTA), which favors Nigeria’s economy greatly, Nigeria can take advantage of this to become an agricultural powerhouse in Africa.
For example, Africa has the lowest intra regional trade amongst the seven continents. Indeed, 68% of Europe’s trade is within the continent. However, Africa does more trade with non African nations than we do amongst each other. Our intra-continental trade is an abysmal 18%. This must change and Nigeria is key to altering this sad state of affairs.
Within the Agricultural sector, the African continent in 2014, earned $2.4 billion from the export of coffee to Europe. That sounds impressive. However, one country alone, Germany, made $3.8 billion from re-exporting Africa’s coffee in 2014. This trend continued into 2015, 2016 and has not changed to date. What is it that Germany does to add value to the coffee, cocoa, and other produce that they buy from Africa that we cannot do in Nigeria? Nigeria can easily become a value-added re-exporter of African coffee to the world.
Ditto for tea, cocoa, wheat, sugar cane, and other cash crops. There are none of these products that I have mentioned that Nigeria cannot either grow in commercial quantities or add value to, in the same way other industrialized economies are doing.
I should know because I am already practicing what I am advocating. I have multiple profitable farms and other businesses in the agricultural value chain.
With about 60% of its land assessed as arable, I truly believe that Nigeria is capable of becoming the food basket of the rest of Africa, and in the process, it can capture a sizable portion of the $48 billion that goes towards food imports in Africa. That money should be circulating within Africa, strengthening our currencies, growing our GDPs, and enriching our people.
I was in Benin Republic recently and I was informed by one of the most successful industrialists in the country that Benin buys its cement from China. Why should a country that shares land borders with Nigeria have to import cement from China 7000 miles away, when Dangote cement is perfectly able, and I am sure willing, to provide the same product at a competitive price?
Is this not what the AFCTA agreement is meant to promote? Why would Nigeria maintain an insane policy of border closures at a time it desperately needs them open to promote trade?
Now is the time for Nigeria to make those hard decisions it has postponed for far too long otherwise the alternative is an apocalyptic scenario we would rather not entertain.
We must, as nation, begin to invest our resources wisely in order to maximize dividends. We must liberalize our land tenure system to make it possible and easy for some of the 27 million unemployed Nigerians to become farmers, even as sharecroppers.
Last year, Ethiopia mobilized its 100 million strong population to plant 350 million trees in 12 hours (a world record). Nigeria can similarly mobilize its population of twice that number to plant billions of cash crops through the planting season. It is possible. I have repeatedly charged my farm associates to sow seeds and they have done so successfully.
When the huge opportunities of agriculture are combined with a rejuvenated manufacturing and MSMEs sectors, then a new era of sustainability and prosperity beckons for Africa.
Nigeria is at the lowest point we have ever been as a nation. We have over indulged on seemingly cheap loans and have quadrupled our foreign debt in just four years. Taking more of such loans will just sink our country deeper and deeper into a quagmire. What is certain is that we can not continue with things the way they are now, except we want to ensure an implosion of our dearly beloved nation.
We must cut our coat, not according to our size, but according to our cloth. Our Presidential Air Fleet of almost 10 planes should go. Our jumbo budgets for our legislature must go. The planned $100 million renovation of our Parliament must be cancelled. We cannot be funding non necessities with debt and not expect our economy to collapse. Our civil servants must come to the realization that Nigeria cannot sustain its size and profligacy. The same cost saving measures must be adopted by the states and councils government.
From henceforth, our energies, resources and focus, must be on how we can diversify our economy, not on how we can increase our expenditure.
-



 News2 days ago
News2 days agoIkpe Hails Mbala’s ‘Rebirth’ As Afurobi Commends Community Drive at Secretariat Commissioning
-



 GRPolitics5 days ago
GRPolitics5 days agoSenator Aishatu Binani Defects to NDC
-



 News5 days ago
News5 days agoTinubu to Travel to Kenya, Rwanda and France from May 2
-



 News5 days ago
News5 days agoMay Day 2026: Sanwo-Olu Approves N50,000 monthly economic relief package for workers






