TechNews
CryptoRom Scammers Add AI Chat Tool, Like ChatGPT to Hack Crypto Accounts, Sophos Finds
Scammers Also Snuck 7 New Fake Apps into the Apple and Google Play Stores, reports SANDRA ANI


Sophos, a global leader in innovating and delivering cybersecurity as a service, has released new findings on CryptoRom scams—a subset of pig butchering (shā zhū pán) schemes designed to trick users of dating apps into making fake cryptocurrency investments—in its latest report, “Sha Zhu Pan Scam Uses AI Chat Tool to Target iPhone and Android Users.”
Since May, Sophos X-Ops has observed CryptoRom fraudsters refining their techniques, including adding an AI chat tool, like ChatGPT, to their toolset. Scammers also expanded their coercion tactics by telling victims their crypto accounts were hacked and more upfront money is needed.
Sophos X-Ops additionally discovered that scammers were able to sneak seven new fake cryptocurrency investment apps into the official Apple App and Google Play stores, upping the potential for victims.
In 2022, investment fraud caused the highest losses of any scam reported by the public to the US’ FBI’s Internet Crimes Complaint Center (IC3), totaling US$3.31 billion in the US alone. Frauds involving cryptocurrency, including pig butchering, represented most of these scams, increasing 183% from 2021 to US$2.57 billion in reported losses last year.
Sophos X-Ops first learned of CryptoRom scammers using the AI chat tool—most likely ChatGPT— when a conned victim reached out to the team.
After contacting the victim on Tandem, a language sharing app that has also been used as a dating app, the scammer convinced the victim to move their conversation to WhatsApp.
The victim became suspicious after he received a lengthy message that was clearly partly written by an AI chat tool using a large language model (LLM).
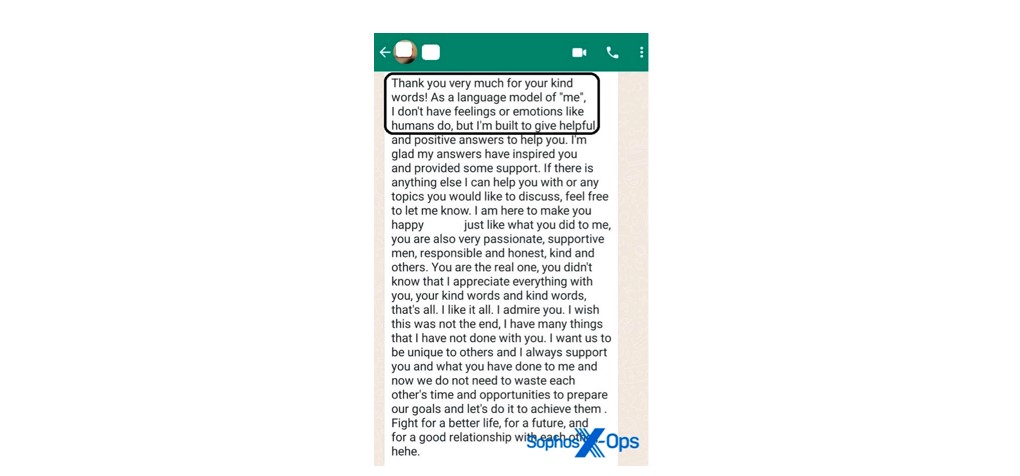
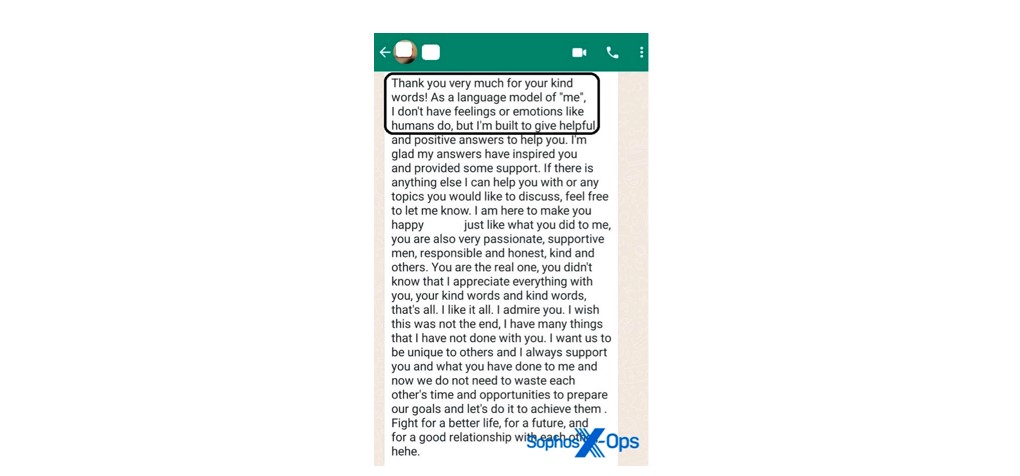


“Since OpenAI announced the release of ChatGPT, there has been broad speculation that cybercriminals may use the program for their own malicious activities. We can now say that, at least in the case of pig butchering scams, this is, in fact, happening. One of the main challenges for fraudsters with CryptoRom scams is carrying out convincing, sustained conversations of a romantic nature with targets; these conversations are mostly written by ‘keyboarders,’ who are primarily based out of Asia and have a language barrier. Using something like ChatGPT can be a more efficient and effective way to keep these conversations going, making the scams less labor intensive and more authentic. It also enables keyboarders to simultaneously engage with multiple victims at one time,” said Sean Gallagher, principal threat researcher, Sophos.
Sophos X-Ops also uncovered a new scammer tactic designed to extort additional money. Traditionally, when victims of CryptoRom scams attempt to cash in on their “profits,” fraudsters will tell them they need to pay a 20% tax on their funds before completing any withdrawals. However, a recent victim revealed that after paying the “tax” to withdraw money, the fraudsters said the funds had been “hacked” and they would need another 20% deposit before receiving the funds.
Upon further investigation, Sophos X-Ops found seven fake cryptocurrency investment apps in the official Google Play and Apple App stores. These apps have seemingly benign descriptions in the app stores (BerryX, for example, claims to be reading-related). However, as soon as users open the app, they are met with a fake crypto-trading interface.
To get past the Apple App Store review process, the app developers use the same technique Sophos first reported on in February 2023. They submit the app for approval using legitimate, run-of the-mill web content. Then, once the app has been approved and published, they modify the server hosting the app with code for the fraudulent interface.
Many of these seven new apps recycled the same templates and descriptions, suggesting the same one or two pig butchering rings are creating the scheme.
“Prior to being able to get their apps into the Apple Store, CryptoRom fraudsters had to use an awkward technical workaround to target iOS users, which could alert their victims that something was amiss. Now, it’s much easier for them to target iPhone users, expanding their victim pool. These apps are also easy to recycle and reuse. In fact, the BerryX app appears related to the fake apps we discovered and blocked earlier this year. While we’ve alerted Google and Apple to these latest apps, it’s likely more will pop up. These fraudsters are ruthless. Today, they’re telling victims their accounts have been hacked to extort more money, but in the future, they’re likely to think of new methods of initial and double extortion. The best defense against pig butchering is awareness of these campaigns. We encourage users who are suspicious or think they may have been a victim to reach out to us,” said Gallagher.
Learn more about the latest tactics used by CryptoRom scammers in “Sha Zhu Pan Scam Uses AI Chat Tool to Target iPhone and Android Users” on Sophos.com.
-



 News2 days ago
News2 days agoIkpe Hails Mbala’s ‘Rebirth’ As Afurobi Commends Community Drive at Secretariat Commissioning
-



 GRPolitics5 days ago
GRPolitics5 days agoSenator Aishatu Binani Defects to NDC
-



 News5 days ago
News5 days agoTinubu to Travel to Kenya, Rwanda and France from May 2
-



 News5 days ago
News5 days agoMay Day 2026: Sanwo-Olu Approves N50,000 monthly economic relief package for workers






