GRTech
OBUNO IoT Engine, Powerful Tool To Launch Nigeria into $19tr IoT Market- Dr Agu
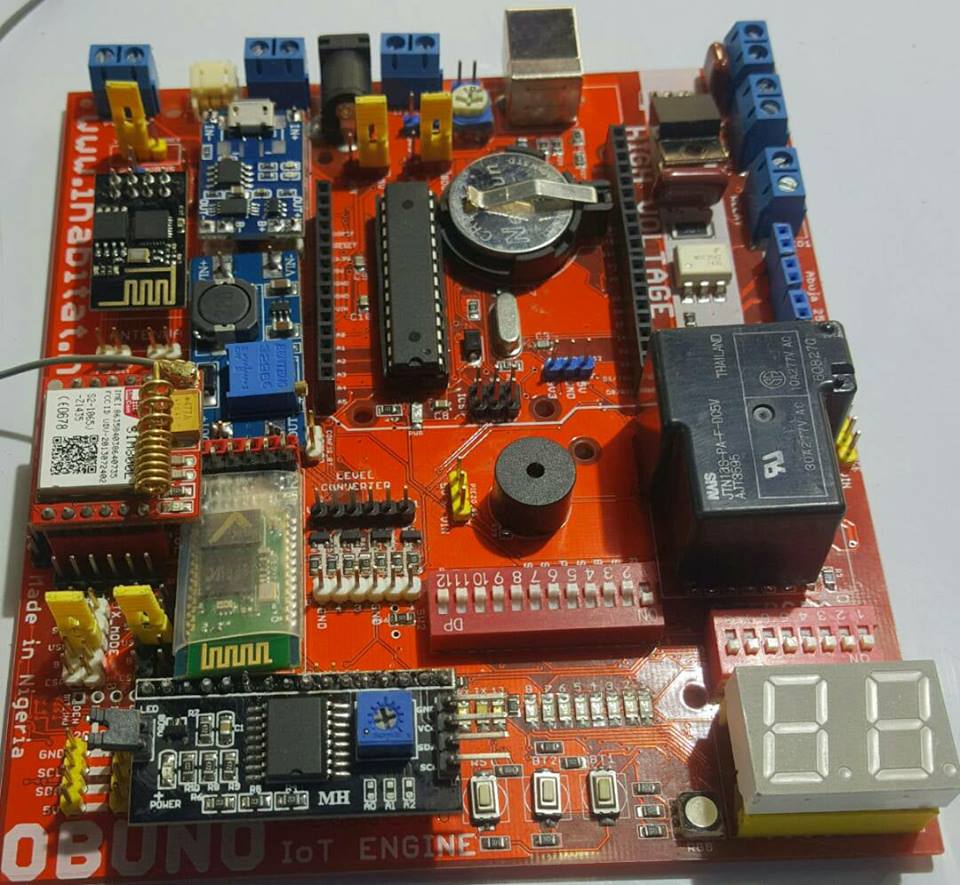
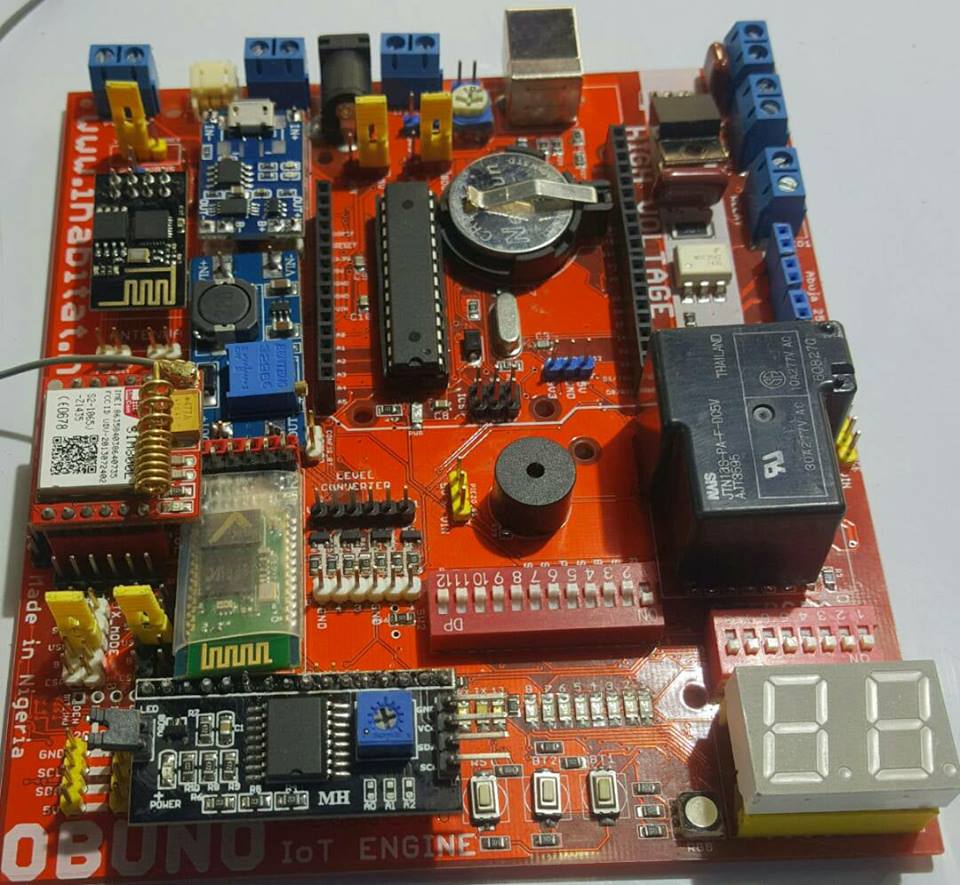
In the new global technology order termed ‘fourth Industrial age’, the Internet of Things (IoT) is identified to be a key enabler with an estimation of more than 24 billion IoT devices on earth by 2020 translating to approximately four devices per person. To this end, ‘OBUNO IoT Engine’, a wholly made-in-Nigeria IoT board with a sea of possibilities, was launched by an NGO – Innovation Habitat Initiativefor Indigenous Technology, as a launchpad for the nation into the emerging technology economy.The Board adopts a modular and scalable architecture that addresses challenges facing the IoT adoption, adaptation and deployment in Africa, especially in Nigeria; in diverse areas such as e-Government, eHealth, fleet management, telematics, banking & financial services, utilities & service providers, eAgric, elearning, amongst others.
Dr Agu Collins Agu, a Mentor at Innovation Habitat Initiative for Indigenous Technology, who midwifed the OBUNO IoTEnginehighlighted, in a document obtained by Nigeria CommunicationsWeek, the increasing need to fast track capacity development in emerging technologies such as IoT through hands-on training and workshops. This, he said is to demystify the underlying technology and building blocks which translates to skills acquisition that will transition Africa into an outsourcing destination and manufacturing economy.
DrAgu Collins Agu, who doubles as Director of Corporate Planning & Strategy Department of the National Information Technology Development Agency (NITDA), said, As the world enters into the 4th Industrial age, the Internet of Things (IoT) is identified to be a key enabler with an estimation of more than 24 billion IoT devices on Earth by 2020 translating into approximately four devices per person; “As we approach that point, $6 billion is predicted to flow into IoT solutions, including application development, device hardware, system integration, data storage, security, and connectivity and these investments will generate at least $13 trillion by 2025”.
“The fact remains that the market share of IoT by 2020 will be 19 trillion USD with over 50 billion devices connected. Now the question is: Do we engage the usual Adoption Model or get innovative and engage the Adaptation Model.“I would recommend the later; underscoring the need for scarce skills development & acquisition to enable us achieve Technology Adaptation and Customization (TAC), which will be a big shift from the traditional Technology Adoption that has kept us as consumers with no digital sovereignty”.
He also argues that the introduction of local content policy was a bold step by Nigeria to leapfrog technological developments.“Nigeria has woken up to these challenges by the introduction of the Local Content Policy in ICT and The Executive Order, mandating the patronage of indigenous products and services with NITDA as the Watchdog. I must say that the countdown has commenced for massive explosion in hardware development such as the OBUNO IoT Engine to drive the penetration and application of IoT. Enforcement of the laws will be a major catalyst in materializing start-ups to drive the knowledge economy”, Agu said.
He further described OBUNO® IoT Engine as the perfect platform that brings both professionals and students (industry and academia) to explore the possibility of talking to the cloud, creating great opportunities to assimilate smart technologies, design the next big thing and solve unique problems. “It is maker friendly and fully compatible with Arduino IDE and peripheral modules. OBUNO® IoT Engine, an end-to-end platform helps IoT developers avoid tunnel vision and its consequences by providing a comprehensive set of hardware and software components that easily combine into complete IoT applications, providing developers with a head start on their custom designs”.
As IoT applications bring a particularly tight convergence between hardware and software components, requiring developers to account for myriad details in each domain; “OBUNO® IoT Engine creates a single platform designed to facilitate that convergence through an ecosystem that provides a unified platform of components and services designed to address the entire IoT application hierarchy. “At the lowest layers of the IoT hierarchy, hardware modules support high-performance data acquisition and signal processing while providing multiple wireless connectivity options”, Agu explained.
OBUNO® IoT Engine is slated for launch across the six geopolitical zones of Nigeria.
GRTech
Identity Management Day: Sophos Warns Against Data Breaches Linked to Identity Theft
REPORTER: Sandra Ani


79% of data breaches are linked to identity theft and cost businesses an average of $4.5 million, according to reports from the Identity Defined Security Alliance (IDSA) and the Ponemon Institute.
Additionally, the 2025 edition of the Sophos Active Adversary Report reveals that the average time between the start of an attack and data exfiltration is only 72.98 hours (3.04 days), while the average time between exfiltration and attack detection is just 2.7 hours.
Cyberattacks are becoming increasingly fast, and the longer a compromised identity remains active, the greater the potential damage.
In light of this, Sophos, one of the world’s leading providers of innovative security solutions designed to neutralize cyberattacks, is taking advantage of Identity Management Day, which takes place on Tuesday, April 8, 2025, to remind businesses of the best practices they should follow to manage and secure digital identities.
Cybercriminals can use a compromised identity to access confidential information, steal data, move laterally within the organization, and launch further attacks.
It is therefore crucial to take immediate action to contain breaches and minimize their consequences.
In this context, automation plays a key role by enabling organizations to respond quickly and effectively to identity-related threats.
Five Automated Measures to Protect Against Identity Theft
1. Disable the User
When an identity breach is detected, one of the first steps is to disable the compromised user account. By preventing the attacker from using the stolen identity to access company systems and data, this measure outpaces the hacker and helps contain the breach.
Automation significantly speeds up this process. With automated response tools, businesses can quickly identify compromised accounts and disable them in real-time. This reduces the attack window and minimizes potential damage.
2. Force Password Reset
Passwords are often the first line of defense against unauthorized access attempts. In the event of an identity breach, it is essential to immediately force a password reset for the compromised account to prevent hackers from using stolen credentials.
Automated rules can be set up to trigger an instant password reset as soon as a breach is detected. This saves time and ensures that the reset process is initiated without delay, reducing the risk of further unauthorized access attempts.
3. Force Multi-Factor Authentication (MFA) Reset
Multi-factor authentication (MFA) adds an extra layer of security by requiring users to enter a verification code in addition to their password. If an identity breach occurs, it is crucial to reset MFA for the compromised account. This means that the user will have to re-authenticate using their MFA tool, which automatically invalidates any stolen authentication tokens the attacker may have acquired.
Automated rules can trigger the refresh of MFA tokens, ensuring that compromised accounts are quickly reauthenticated. This prevents cybercriminals from using stolen authentication tokens to access company systems.
4. Lock the Account
Locking a compromised account prevents hackers from attempting to use it until the issue is resolved. This also gives the organization time to investigate the breach and apply the necessary corrective measures.
Automation streamlines the account locking process, allowing businesses to lock compromised accounts as soon as a breach is detected. This immediate response helps contain the breach and blocks further unauthorized access attempts.
5. Revoke Active Sessions
In addition to disabling the user account and forcing a password reset, it is essential to revoke all active sessions associated with the compromised identity. This ensures that the attacker is immediately logged out of all systems they accessed using stolen credentials.
Automated actions can be configured to revoke active sessions in real-time, instantly disrupting any unauthorized access. This is a critical measure to neutralize the breach and prevent further malicious activity.
For more information, please visit: https://www.secureworks.com/blog/5-critical-response-actions-for-an-identity-breach
GRTech
Samsung Expands Accessibility with Local Language Integration on Galaxy S25, A56, A36, and A26 Devices
By SANDRA ANI


Samsung Electronics has taken a bold step in enhancing user experience and inclusivity by introducing Hausa, Igbo, and Yoruba as official language options on selected Samsung Galaxy devices.
The feature, which is now available on the Galaxy S25, A56, A36, and A26 devices, reaffirms Samsung’s commitment to delivering innovative technology that speaks the language of its users.
With this groundbreaking update, Samsung users across Nigeria can now navigate their smartphones in their preferred local language, making technology more accessible, while also upholding our cultural heritage.
A Celebration of Culture and Technology
To mark the launch, Samsung hosted a cultural-themed press briefing featuring traditional music, local cuisine, and a showcase of the new language feature. Employees and guests attended in traditional Yoruba, Igbo, and Hausa attires, celebrating Nigeria’s rich cultural diversity.
Samsung also announced plans to expand local language support to more devices in the near future, reinforcing its dedication to making technology more inclusive for African users.
Empowering Users Through Language
The integration of Hausa, Igbo and Yoruba on Samsung devices reflects the brand’s mission to bridge the digital gap and enhance user engagement. Speaking at the press conference, Oge Maduagwu, Head of Marketing, Samsung Electronics West Africa, said, “At Samsung, we understand that technology is most powerful when it is accessible to all. By incorporating our local Nigerian languages, we are making our devices more intuitive and relatable, ensuring that millions of Nigerians can interact with their smartphones in the language they love and understand best”.
Seamless Language Transition on Galaxy Devices
Stephen Okwara, Head of Product Management, Samsung Electronics West Africa added, “The new local language feature is designed to deliver a seamless user experience, allowing customers to easily switch between languages. Users can activate Hausa, Igbo, or Yoruba on the Galaxy S25, A26, A36, and A56 by navigating to:
Settings > Language & Input > Select Language
“This update enhances smartphone usability, particularly for those who prefer their native language over English, ensuring greater digital inclusivity, enhancing digital literacy and encouraging more users to engage with technology in their native tongues”, he concluded.
Availability
Customers can visit all Samsung Experience Stores or authorized retailers in Nigeria to learn more and experience the feature firsthand.
TechNews
NITDA DG Inaugurates National Technical Working Group on Cloud Infrastructure
REPORTER: Sandra Ani


In a significant move to bolster Nigeria’s digital infrastructure, the National Information Technology Development Agency (NITDA) has inaugurated the Technical Working Group (TWG) on National Cloud Infrastructure.
This initiative aims to enhance local cloud capabilities, attract hyper-scale investments, and position Nigeria as a leading technology hub in Africa.
Speaking at the inauguration, NITDA’s Director-General, Kashifu Inuwa, CCIE, emphasised the need for accurate data and regulatory frameworks to support these initiatives, necessary for Nigeria to control its digital infrastructure, data, and technological future noting that,
“Without this foundation, we cannot achieve true digital sovereignty. Our goal is to build an ecosystem where both local data centre providers can scale, and global hyper-scalers see Nigeria as a viable investment destination.”
While identifying lack of accurate data on Nigeria’s IT infrastructure as significant challenge, Inuwa noted that while Africa comprises nearly 19% of the world’s population, it hosts less than 1% of global data centres.
“This disparity, coupled with limited insights into Nigeria’s existing IT capacity, hampers investment efforts and without clear data on our infrastructure, attracting investment becomes challenging,” he said.
The NITDA boss maintained that, to address this, NITDA commissioned comprehensive research to assess Nigeria’s digital landscape which findings have highlighted the need for improved regulatory frameworks, clearer investment incentives, and stronger public-private collaboration. He added that subsequently upon this, NITDA has engaged global consultants to redefine strategies for cloud development.
As the TWG embarks on its mission, NITDA urges industry experts, policymakers, and stakeholders to contribute their expertise and resources. “With collective effort, Nigeria can emerge as the premier digital hub for West and Central Africa,” Inuwa concluded.
While corroborating the Director General’s point of views, Acting Director of Regulation and Compliance, Barrister Emmanuel Edet, underscored the importance of regulatory intervention in fostering a robust digital economy.
“Our objective is to establish policies and legal frameworks that support cloud development, enabling us to securely host and manage our data. This is crucial for the growth of our digital economy, he said.”
He also highlights the necessity of capacity building, stating that, “Equipping ourselves with top-tier training and expertise is essential to fully leverage digital technologies.” Barrister Edet called on all stakeholders to actively participate in shaping Nigeria’s digital future.
“Collaboratively, we must develop a framework that reflects our national interests, and it should be widely accepted. This effort will define Nigeria’s role in the global digital arena, he observed.
The TWG will help in the drive to attract hyperscale investments and enhance local cloud capabilities by proffering measures to encourage the use of accurate data, recommend the enactment and compliance to enabling policies.
Members of the TWG which includes Google, AWS, IBM, Oracle, Microsoft, HUAWEI Cloud, Equinix, Kasi, Rack Centre, Africa Data Centres, several other data centre operators and the Nigeria Data Protection Commission expressed support and readiness to volunteer and contribute resources.
-



 Spotlight4 days ago
Spotlight4 days ago“Jesus + Nothing Worship” Leaves Lasting Impact, Amplifying the Message of Christ’s Sacrifice and Resurrection
-



 Finance3 days ago
Finance3 days agoPAFON 2.0: Experts Highlight Ingredients for Accelerated Financial Inclusion in Nigeria
-



 News4 days ago
News4 days agoEmulate Christ’s virtues, Glo urges Christians at Easter








