GRTech
President Buhari Calls For Overhaul Of National Strategy On Cybercrime
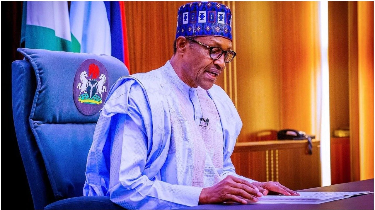
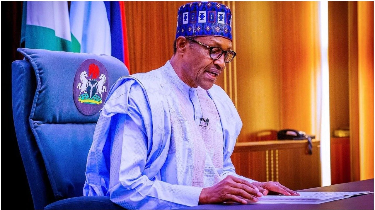
President Muhammadu Buhari Tuesday in Abuja called for an overhaul of the national strategy on cyber security, urging more emphasis on exploring the internet for economic growth opportunities, enhancement of knowledge and mitigation of crime.
“I urge the National Security Adviser to continue to coordinate the efforts of all stakeholders to ensure that our Internet and cyberspace are used for the enhancement of national security and economic progression,’’ the President said at the launch of the National Cybersecurity Policy and Strategy (NCPS) 2021.
“I am confident that, together, we can pave the way for the creation of new opportunities to usher Nigeria into a bright future driven by a prosperous cyberspace and digital economy.’’
The President noted that the Federal Government had taken some major policy decisions to increase penetration of the internet in the daily lives of citizens, particularly for the utilitarian purpose, with launch of National Broadband Plan 2020 – 2025 in March 2020; National Digital Economy Policy and Strategy 2020 – 2030; National Identity Program, Treasury Single Account and Bank Verification Number schemes.
“All these initiatives serve as enablers for tackling many of the economic and security challenges facing our country while also providing us with the platform to improve accountability and transparency in our unwavering resolve to tackle corruption.
“However, like many other countries across the globe, the growth and development of the internet is accompanied by significant problems. We are witnessing a rise in threats posed by cybercriminals, online financial fraudsters and cyber terrorists who use the internet to cause apprehension,’’ the President said.
He added that the internet and social media have witnessed a surge for propagation of hate speech, fake news, seditious and treasonable messages, as well as the risks of breaches to personal information and government sensitive data.
“It is almost impossible to overstate the challenges. Some global events such as the rapid emergence of new technologies, the outbreak of the COVID-19 pandemic and the advent of 5G technology, have further widened the scope and diversification of these cyber threats.
“In October 2020, we all witnessed an escalation in the use of the social media for dissemination of subversive messages and incitement of violence which played a part in heightening tensions, causing unrest and spurring widespread acts of looting and destruction across the country.’’
President Buhari said the Federal Government had been proactive, over the past couple of years, in taking steps to ensure progressive use of internet and cyberspace.
“In 2014, the maiden National Cybersecurity Policy and Strategy was developed to provide the necessary roadmap for the realisation of our national cybersecurity programme. This national effort paved way for Nigeria to reach numerous cybersecurity milestones over the past six years.
“Therefore, in order to build on this achievement and reposition ourselves for enhanced engagement in cyberspace, it became expedient to review the National Cybersecurity Policy and Strategy 2014 and develop a comprehensive National Cybersecurity Policy and Strategy 2021 for the common good of our country.’’
According to the President, the National Cybersecurity Policy and Strategy 2021 will provide us with the necessary platform to effectively confront the dynamic nature of threats in our cyberspace.
“The document will also provide the framework that would enable us to harness the efforts of our private sector, academia and industry towards progressive economic and national development.
“To this end, the document will provide the platform for technical education, digital skills acquisition and indigenous technology production, thereby creating job opportunities for our youth and supporting our resolve to alleviate poverty and boost our economy.’’
In his remarks at the event, the National Security Adviser, Maj. Gen. Babagana Monguno (rtd), said there had been a surge in the use of the internet, especially during the COVID-19 lockdown around the world, with increasing waves of crimes, irregular migration and threats to border security.
The NSA noted that many platforms including banking, communication and military had come under more threat, with personal information easily distorted and explored, necessitating a review of the 2014 National Cybersecurity Policy and Strategy (NCPS).
He said the reviewed document will work towards mitigating the “suffocating presence and unpredictable threats’’ of cybercrimes.












